Sign up to uncover the latest in emerging technology.
Okta may be adding some chains to its cybersecurity approach.
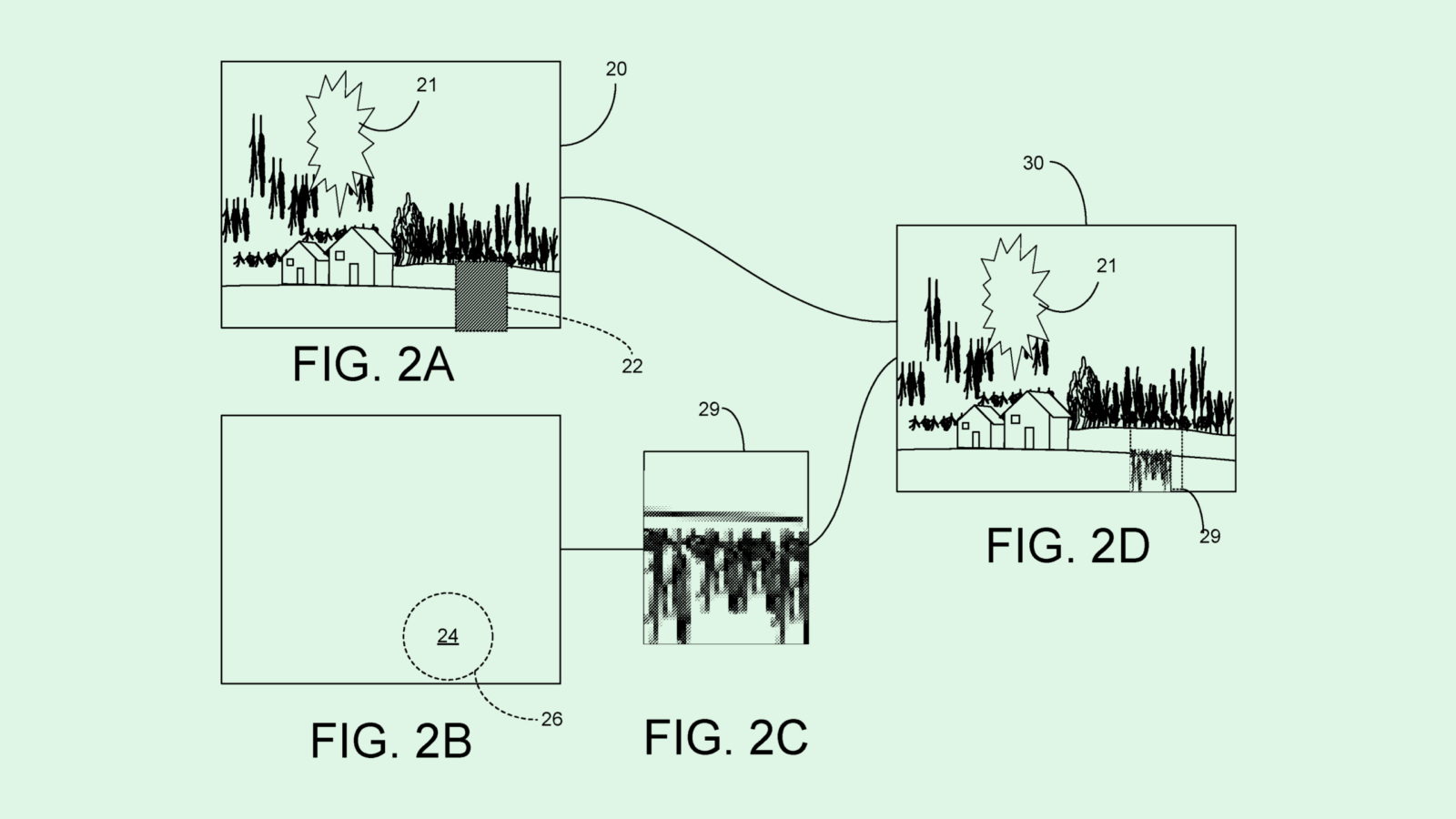
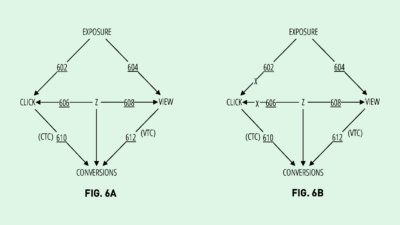
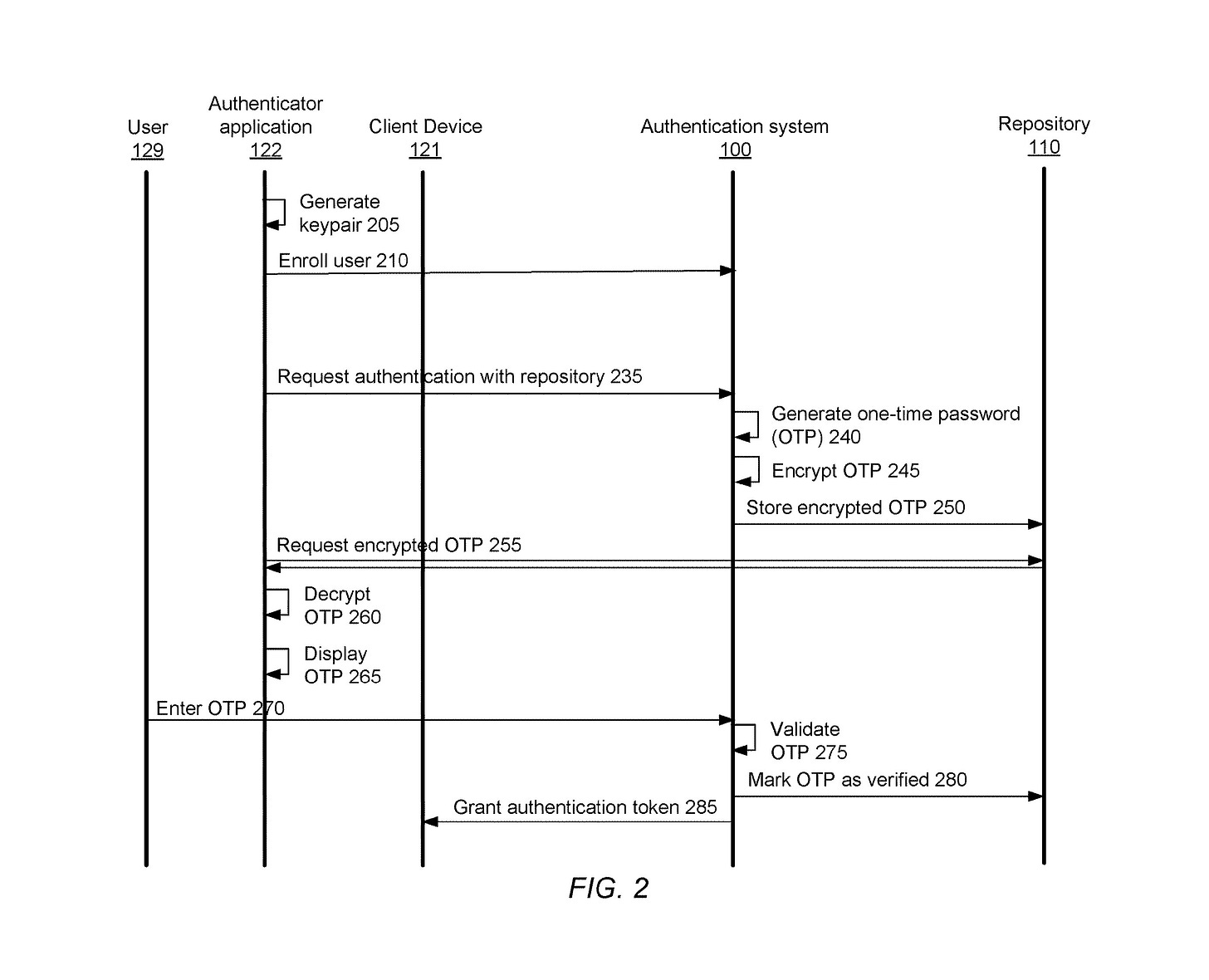
The company filed a patent application for a technique to deliver one-time passwords via blockchain for multi-factor authentication. To generate and distribute one-time passwords, this tech employs a “decentralized secure repository,” or essentially a blockchain-based digital storage unit that’s made up of different systems controlled by multiple organizations. In order for an attacker to breach this repository and tamper with the password system, they’d need to get through the systems of multiple organizations, Okta noted.
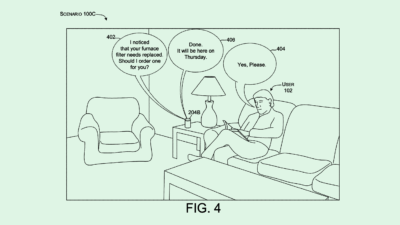
To receive this password, a user has to verify their identity in some way (though Okta didn’t go into detail on how). Once they’re verified, they receive an “authentication token” that allows them access to the repository server and get the password.
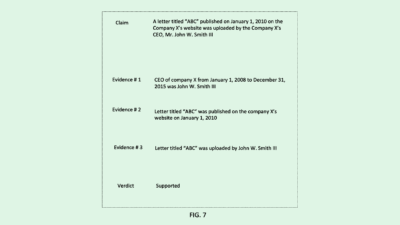
The one-time password is double-encrypted, locked down both within the repository and when transmitted between systems, thereby “thwarting attempts at eavesdropping. The repository itself also comes with enhanced security features by virtue of being a blockchain-based system, including “tamper-proofness,” or the inability to modify data within it, and auditability, aka the power to see any activity involving the data.
Okta said that conventional means of delivering one-time passwords come with a number of shortcomings, including a lack of encryption and a loss of privacy when delivered over text or email, as those systems can easily be compromised by outside attackers.
These systems also “typically lack a way to determine when users’ one-time passwords have been used, thus preventing users from determining whether unauthorized parties have managed to gain access to the system and obtain one-time passwords in their names,” Okta noted.
Given Okta’s core business is cybersecurity and identity management, it adds up that the company is researching new ways to keep client logins secure. But Okta has had its own run-ins with cybersecurity breakdowns in the past year.
The company faced three separate security breaches in 2022: one in March, by the notorious Lapsus$ hacking group; one in August, in which hackers used Twilio to intercept Okta one-time passwords; and one in December, in which its source code was stolen from GitHub repositories. While this tech could be served up as a service for its own customers, the company may want ways to batten down its own hatches.
However, the tech that Okta outlines in its patent seems like just the beginning, said Jordan Gutt, head of web 3.0 technologies at The Glimpse Group. Gutt said that the patent could foreshadow a deeper interest in self-sovereign identity, a type of identity management that gives users or organizations complete control over their digital identity, and has blockchain as a core tenet. (The company currently partners with Entrustient for this type of identity tech).
“On an enterprise level, it’s great to see them leveraging the benefits of blockchain like immutability and the distributed ledger,” said Gutt. “But this seems like a foundation to other products that Okta could be working on.”
And while the tech in this patent covers the creation and delivery of the password, it doesn’t seem to cover how it protects the password “once it gets into the user’s hands,” said Ali Allage, CEO of BlueSteel Cybersecurity. Often, security breaches involving one-time passwords aren’t related to failures of the password delivery system itself, Allage said, but rather failures on the client side.
For now, Allage said, “It’s just a highly encrypted way of storing one-time passwords. I think it’s progress. I don’t think it’s the end result.”
Have any comments, tips or suggestions? Drop us a line! Email at admin@patentdrop.xyz or shoot us a DM on Twitter @patentdrop. If you want to get Patent Drop in your inbox, click here to subscribe.